Hackers Took Over — Now Take It Back
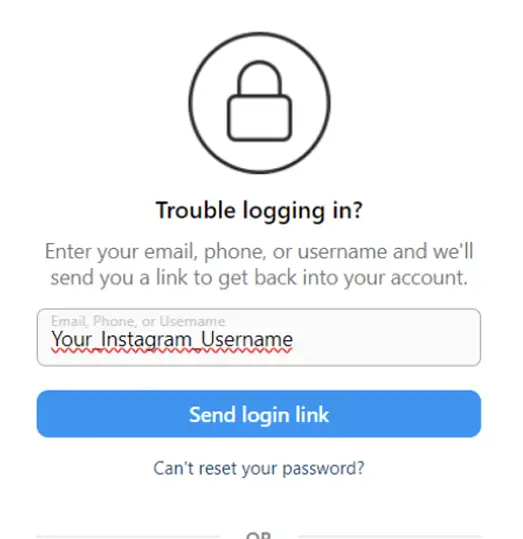
Someone changed your password, swapped your email, enabled their own 2FA. You're locked out of your own account watching a stranger control your identity. Our recovery tool kicks hackers out and hands control back to you — even when they've changed every security setting and locked every door.
What Hackers Do Once Inside
The Complete Takeover Playbook
Experienced hackers work fast. Within minutes they change password, replace email, add their phone number, enable two-factor authentication. Every recovery path Instagram offers now leads to them. Standard recovery is impossible because every verification method confirms the hacker, not you.
Email Swapped Immediately
First thing hackers change is email address. Now every password reset, every security alert, every recovery link goes directly to their inbox. Instagram thinks they're the legitimate owner. You've become the outsider trying to break into "someone else's" account.
Your Identity Becomes Their Weapon
Hackers don't just steal accounts — they weaponize them. Scamming your followers, messaging your contacts, posting content under your name. Every minute they maintain control damages your reputation. Some hold accounts ransom. Others sell access to third parties. Speed of recovery matters.
Evict Hackers Permanently
Remove unauthorized access and reclaim your Instagram account within hours. Even when hackers changed everything — password, email, phone, 2FA — recovery is possible.